Chrome 80 launched February 4, 2020 with new default settings for the SameSite cookie attribute. These changes may dramatically impact third-party cookie tracking, loosely akin to Safari's ITP.
This article explains what SameSite attributes are and what you need to do as a publisher to continue monetizing your ad platform.
What is the SameSite attribute?
The SameSite attribute tells browsers when and how to fire cookies in first- or third-party situations. SameSite is used by a variety of browsers to identify whether or not to allow a cookie to be accessed.
SameSite has made headlines because Google’s Chrome 80 browser enforces a first-party default on all cookies that don’t have the attribute set. This could lead to repercussions if companies who rely on third-party cookie requests didn’t make changes by the February 4 deadline.
Can you break that down for me?
Sure thing! Values for the SameSite attribute include "strict", "lax", or "none":
- "lax" enables only first-party cookies to be sent/accessed
- "strict" is a subset of "lax" and won’t fire if the incoming link is from an external site
- "none" signals that the cookie data can be shared with third parties/external sites (for advertising, embedded content, etc)
For example, I have a social community site and I use cookie IDs to store user information. If my first-party cookies are set to "lax", I can always access that data. If my first-party cookies are set to "strict", I can’t access data if the incoming link is from an external site. For example, if a user visits my site directly from say, CNN.com, I’m unable to read the cookie.
A "strict" setting is relatively uncommon for publishers but provides greater security for financial institutions and other risk-averse companies.
Previously, if SameSite wasn’t set, it defaulted to "none" - enabling third-party sharing by default. Now, if the SameSite attribute isn’t set, the Chrome default is the first-party "lax" setting.
Here’s an overview of the changes:
AttributeWhen cookie firesDefault modeSameSite=StrictDomain in URL bar equals the cookie’s domain (first-party) AND the link isn’t coming from a third-partyn/aSameSite=LaxDomain in URL bar equals the cookie’s domain (first-party)New default if SameSite is not set'SameSite=None'No domain limitations and third-party cookies can firePrevious default; now needs to specify 'None; Secure' for Chrome 80
It’s worth noting that ‘same company’ doesn’t equal ‘same site’. If a company owns multiple websites, cookies used across those sites would be considered cross-site (third-party) once the cookie’s domain no longer matches that of the site the user is on.
For instance, cookies used to store users’ logins, credit card numbers, and shipping addresses on Gap.com would be considered cross-site if those users click on links to Gap’s other branded sites, such as Athleta.com or BananaRepublic.com.
What do Chrome’s SameSite changes mean for ad tech?
Specifically, Chrome now treats any cookies without the new "SameSite=None; Secure" attribute as "SameSite=Lax", which limits them to first-party contexts.
The impact will be greatest for ad tech vendors that use third-party cookies to track users’ activities across the web - including for retargeting. If they don’t implement these attribute changes, they could lose access to the data that fuels their businesses
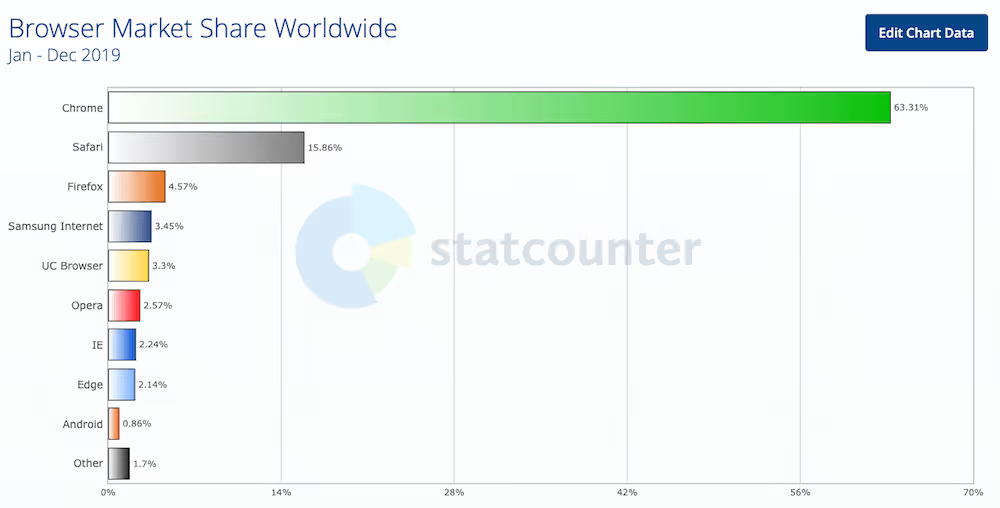
Broadly, Google’s new SameSite attribute is yet another indication of the growing concerns around data privacy. Given Chrome’s global popularity and current 63% share of the browser market, it’s also yet another push for ad tech to improve how it targets consumers and to challenge its longstanding reliance on potentially invasive third-party cookies.
Unlike Apple ITP (Intelligent Tracking Prevention), Chrome doesn't block third-party cookies by default, but it does limit their use to secure, HTTPS connections. This gives Google visibility into what cookies are third-party - opening the possibility they offer an easy future opt-out option.
How do publishers need to prepare?
If you’re a publisher, we recommend auditing, analyzing, and updating your SameSite cookie attributes to avoid diminished results and revenue in Chrome.

If you do nothing, your cookies will default to the "SameSite=Lax" setting and therefore be limited to first-party use in Chrome 80. You may also see inconsistent cookie behavior across browsers and console warnings from Google
For more details on updating your attributes, we recommend Google's SameSite cookie recipes.
What’s next?
We can’t predict the future, but it’s safe to assume that third-party cookies will continue to be controversial in this age of data privacy - and continue to challenge decades-long digital advertising practices.
While these SameSite changes may seem burdensome in the short term, we believe they will ultimately benefit publishers that respect user privacy and monetize via first-party behavioral targeting, contextual targeting, intent targeting, and other tactics
Note: On April 3, 2020, Google announced a temporary pause on its enforcement of SameSite cookie labeling in Chrome 80. Enforcement resumed on July 14, 2020.


